The SecurityBridge industrial firewall is a product for the industrial security sector. The firewall for industrial applications protects industrial automation networks from manipulation and unauthorised access. So espionage and manipulation don't stand a chance, and you guarantee the safety of your staff and the availability of your machine!
SecurityBridge industrial firewall
On the safe side with the SecurityBridge industrial firewall!

Protection extended to industrial automation networks
With its new firmware, the SecurityBridge firewall now offers comprehensive protection for industrial automation networks. Not only does it protect the configurable safe small controllers PNOZmulti and the automation system PSS 4000, it also now enables control over data communication between any other subscribers outside of the Pilz range. The SecurityBridge was developed in line with the secure development process in accordance with the standard IEC 62443-4-1 and also respects the principle of "Zones and Conduits".
“Packet recording” has been added to the extensive diagnostic functions. This can be used to record data communication between subscribers from the secured controller network and the unsecured network. Recording can be restricted to specific communication relationships to enable you to analyse data more efficiently. That saves you valuable time during diagnostics!

Also protect virtual access to your machine!
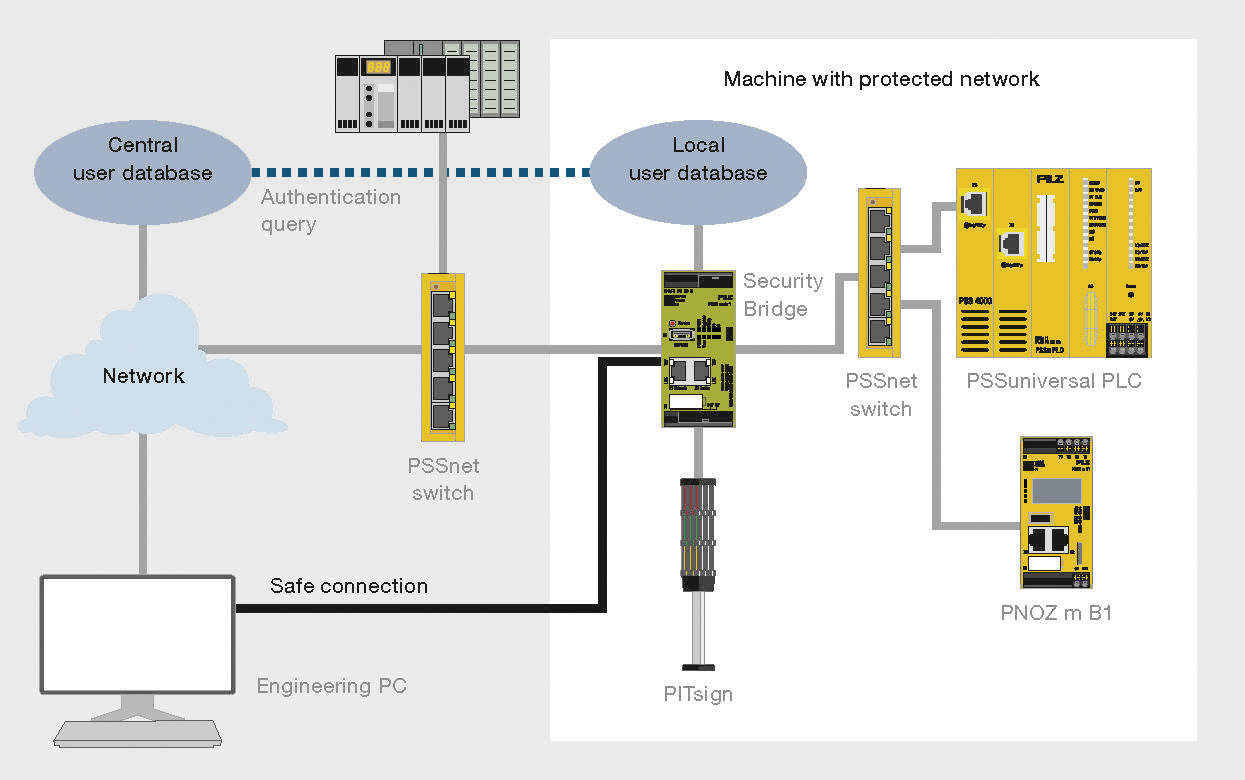
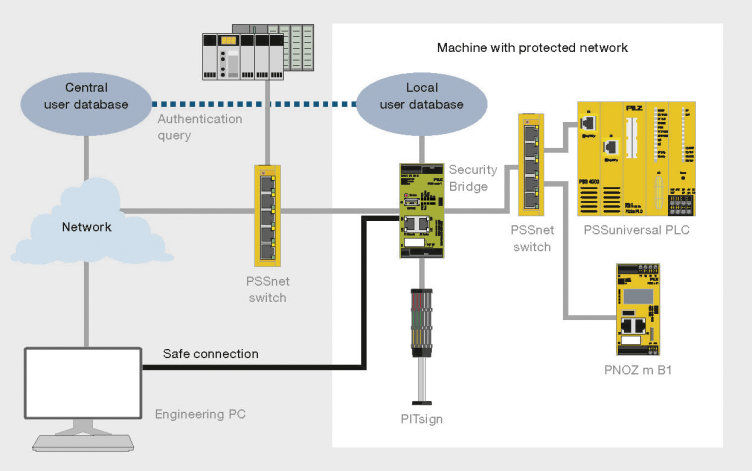
Physical access to machinery is clearly defined in the Machinery Safety Directive. For example, a safeguard on a gate ensures that a person cannot move within the danger zone until the machine is in a safe state. The SecurityBridge industrial firewall ensures that only authorised persons have access to the plant via the network. As a firewall it monitors communication with the controller and controls the data flow. You can also use SecurityBridge to store user rights; these define which staff members may access which data.

SecurityBridge wins GIT Security Award 2019

The application firewall SecurityBridge was awarded 3rd place in the GIT SECURITY Award. The award was presented on 27 November 2018 at SPS IPC Drives in Nuremberg.
The GIT SECURITY AWARD is awarded nationally and internationally. Three innovative products with the most votes were selected from a total of six categories. SecurityBridge was competing in "Category A – IT-Security and Safety for Automation, Cyber Security”. It convinced our customers, partners, market players and readers of the magazines GIT SICHERHEIT, GIT SECURITY and messtec drives Automation and won through against 14 more finalists.
This is how to use SecurityBridge
The SecurityBridge can be connected upstream of the PNOZmulti base unit, the PLC controller PSSuniversal PLC or any other subscribers outside of the Pilz range. The connection between PC and device is therefore protected. Only users with the relevant permission can make changes to a project’s configuration. This prevents unauthorised access to the secured network. In this way, data transmission between the Client PC and SecurityBridge is safe from eavesdropping and manipulation.
The SecurityBridge also controls the process data traffic and monitors the integrity of the safety system. Changes to the check sum provide information about changes to the projects in the controller project.
Benefits at a glance:

- Developed in accordance with the standard IEC 62443-4-1
- Simple to install, no need to adjust the network parameters
- VPN connection with role-based user management
- Configuration changes can only be carried out by authorised users
- Increased availability, as only data from permitted communication relationships is approved
- Process data is forwarded in wirespeed with low latency for time-critical applications
- Detects unauthorised changes to the project by verifying the check sum (CRC)
- Comprehensive diagnostic functions
- Simple to configure via a web-based user interface
- Continuous updates are functionally feedback-free for the protected control system
Technical features:
- 2 RJ45 sockets for connection to Ethernet
- VPN Server to establish a VPN tunnel for secure data transfer
- Forwarding rules for IP connections and fieldbuses
- Bypass mode (security functions are temporarily deactivated for diagnostic purposes)
- Setup mode for maintenance work
- Output to display the status of the connections or the operating mode, for example
- Input to trigger certain functions or event messages (e.g. activation of setup mode)
- Bridging mode (enables network security to be extended, without having to change IP address configurations)
- Centralised authentication of users via RADIUS
- USB port to save and restore the configuration on a USB memory
- LED indicators for error messages and diagnostics
- Connection to central diagnostic server via SYSLOG
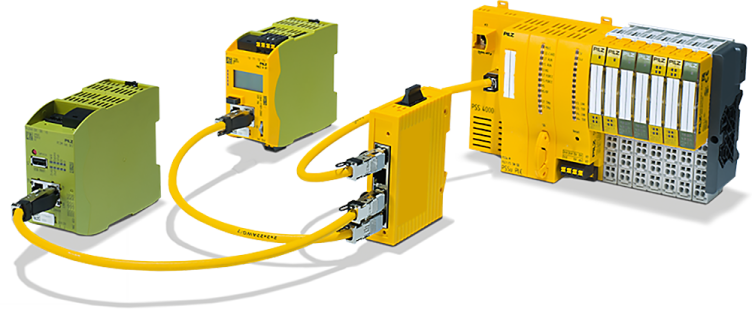
Our product range: Industrial security
Pilz South East Asia Pte. Ltd.
25 International Business Park, #04-56 German Centre
Singapore 609916
Singapore
Telephone: +65 6839 292-0
E-Mail: sales@pilz.sg
Telephone: +65 6829 2920
E-Mail: techsupport-sg@pilz.com